Trojan.Triosir.9 is a plug-in for web browsers designed to display annoying advertisements to users as they browse webpages. From May 2014, this malicious program has been distributed through an affiliate program called Installmonster. Trojan.Triosir.9 is created by Trioris.
One of its modifications is distributed as the VK User Spy plug-in that can supposedly allow users to stealthily view Vkontakte (“ВКонтакте”) messages. This plug-in is presumably developed on the basis of a legitimate browser extension called VKSpy. Cybercriminals even left the names of real application's creators (Evgeniy Zinoviev and Ivan Gusev) in \ldognehopalabhkhpeeedfdeeedfhchg\3.1_0\_locales\ru\messages.json unchanged:
{
"about": {
"message": "О приложении"
},
"about_ez": {
"message": "Евгений Зиновьев"
},
"about_ig": {
"message": "Иван Гусев"
},
"ago_hour_format": {
"message": "%s назад"
}During installation, the system registry is checked for the presence of already installed Trioris applications, including Get-Styles, desktopy.ru, screeny.ru, and other applications. If any of them is detected, installation is aborted. While the malicious program is installed, it connects to the command and control server and uses a list of keywords and properties to determine what websites should not display advertisements and what websites should.
Cybercriminals added a string to the content.js file's code of the original VKSpy plug-in. The string calls the stat.js script that downloads ursp.js. This script, in turn, downloads two additional scripts which generate advertising modules.
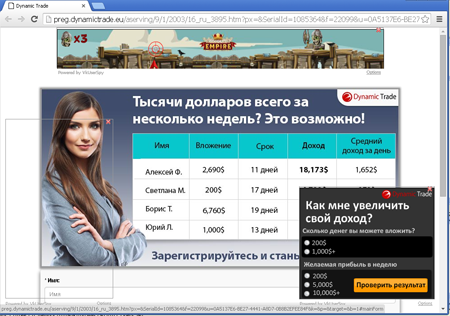
The Trojan displays advertisements on top of webpages browsed by the user. The window with an advertisement has a special button by clicking which the user can close the module. Moreover, there is a sign that says “Powered by VkUserSpy”; at that, the name of the product is first specified in the ursp.js script (in the window._rw_pr_n = "VkUserSpy" variable) and is subsequently used by other scripts.