A malicious program designed to infect ATMs of one international manufacturer. It is distributed in Latin America and is supposedly installed on the system from a bootable CD.
To perform some of its functions, the Trojan utilizes a dynamic library from the ATM’s SDK. The Trojan is installed on the infected system as the NCRDRVPS system service. It saves its configuration data in the config.ini file in the current folder. The log is saved to the Log.txt file.
Once F8, F1, F7, F3, F5, F4, F2 are pressed consecutively, the Trojan’s control panel is displayed on the screen. However, the malware can receive commands even when the panel is not displayed.
In this mode, Trojan.Ploutus.1 can execute the following commands:
- 12340000—test command whose execution results in the display of the “TEST KEYBOARD DATE:” message and the current date.
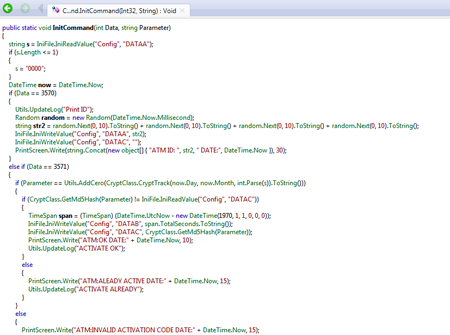
- 12343570—command to generate and display the ID (4 random numbers) and then to enter this value into the DATAA parameter of the configuration file.
- 12343571xxxxxxxx (where xxxxxxxx stands for the key that is calculated based on the current date, month, and ID and completed with additional zeros)—command to withdraw cash at the specified moment of time (valid for 24 hours). The operation time is added to the DATAB parameter of the configuration file. The activation key’s md5 value is entered into the DATAC parameter.
- 12343572xx (where xx stands for the number of bills)—command to empty a cash tray.
If the Trojan’s control panel is displayed, the following keys can be employed to give commands to the Trojan:
- F1—generate and display the ID (4 random numbers) and then add this value to the DATAA parameter of the configuration file
- F2—command to withdraw cash at the specified moment of time
- F3—command to empty a cash tray
- F4—hide the panel
- F5–F8—navigation functions
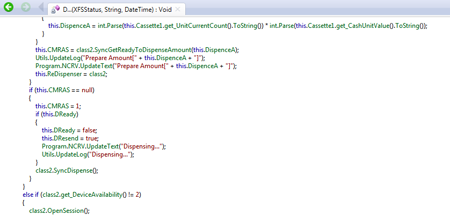
DispenceClass is responsible for emptying a cash tray. The cash withdrawal routine is implemented as follows: