Trojan.Kasidet.1
SHA1:
- 79b863bd3148c84229e81d6c5aed65390a2cba18 rar_sfx.scr
- e37f808d6147022f0ee79c34f80697af86ab571e entroentry.exe
- a673eec895f7009873c400247d056c325935be76 entroentry.unp
- a9e2c692887ad9732d566e6818e32a6a7466d593 payload
A Trojan for POS terminals. It is a modification of Trojan.MWZLesson.
The Trojan is distributed as a ZIP archive that contains a SCR file, which is a self-extracting SFX-RAR archive. This file then extracts, runs entroentry.exe, a malicious application, and saves an empty file named indexoid.txt.
Once launched, the Trojan checks the system for its copy and tries to detect one of the following running processes:
- prl_cc.exe
- prl_tools.exe
- vmwaretray.exe
- vmwareuser.exe
- vboxservice.exe
- vboxtray.exe
- vmsrvc.exe
- vmusrvc.exe
The Trojan attempts to find the following modules in its process:
- api_log.dll
- dir_watch.dll
- pstorec.dll
- vmcheck.dll
- wpespy.dll
- sbiedll.dll
In addition, the Trojan determines whether a debugger or virtual machines are present on the system. If it finds a program that can somehow hinder the Trojan’s operation, Trojan.Kasidet.1 executes the following command in CMD:
ping 127.0.0.1 -n 3 & del “<full path to the Trojan>"
And then it terminates and deletes itself from the system.
To start its malicious activity, it is run with administrator privileges executing the following command for wmic.exe:
process call create < full path to the Trojan >
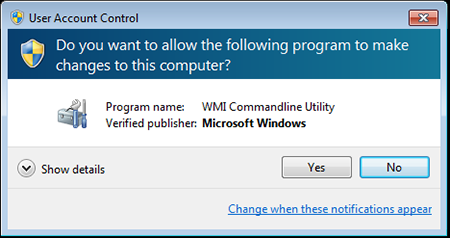
Even though the User Accounts Control (UAC) system demonstrates a warning on the screen, the victim is put off their guard because the running application (wmic.exe) is allegedly developed by Microsoft:
Then wmic.exe runs the Trojan’s executable file.
In Microsoft Windows 8, the Trojan disables SmartScreen and modifies the system registry branch:
[HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer]
"SmartScreenEnabled"="Off"
Then it deletes the following value:
HKLM\SOFTWARE\Policies\Microsoft\Windows\System, EnableSmartScreen
The Trojan modifies the Windows registry to ensure running of its copy.
Like Trojan.MWZLesson, this Trojan executes the following functions:
- Checks the infected computer's RAM for bank card data and sends all acquired bank card data to the command and control server.
- Steals passwords for Outlook, Foxmail, and Thunderbird email applications.
- Incorporates itself into Mozilla Firefox, Google Chrome, Microsoft Internet Explorer, and Maxthon browsers in order to intercept GET and POST requests.
- Upon a command, searches for a particular file on disks—if the file is found, it is sent to the server.
- Updates itself by downloading an executable file from the specified URL. Then the Trojan saves the file to its folder under a random name and runs it. If launched successfully, it removes data, necessary for its autorun, from the registry and tries to delete the original file.
- Saves and removes parameters specified in the system registry.
- Downloads and runs an executable file or a dynamic library that is then loaded to the memory with the help of the regsvr32 /s <file name> command.
- Executes specified commands in CMD.
Unlike Trojan.MWZLesson, C&C server addresses of Trojan.Kasidet.1 are placed in a decentralized domain zone—.bit (Namecoin). It is a system of alternative root DNS servers, which is based on the Bitcoin technology.